Vulnerabilites related to humansignal - label_studio
CVE-2023-47117 (GCVE-0-2023-47117)
Vulnerability from cvelistv5
Published
2023-11-13 20:13
Modified
2025-01-08 21:12
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor
Summary
Label Studio is an open source data labeling tool. In all current versions of Label Studio prior to 1.9.2post0, the application allows users to insecurely set filters for filtering tasks. An attacker can construct a filter chain to filter tasks based on sensitive fields for all user accounts on the platform by exploiting Django's Object Relational Mapper (ORM). Since the results of query can be manipulated by the ORM filter, an attacker can leak these sensitive fields character by character. In addition, Label Studio had a hard coded secret key that an attacker can use to forge a session token of any user by exploiting this ORM Leak vulnerability to leak account password hashes. This vulnerability has been addressed in commit `f931d9d129` which is included in the 1.9.2post0 release. Users are advised to upgrade. There are no known workarounds for this vulnerability.
References
| ► | URL | Tags |
|---|---|---|
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: < 1.9.2post0 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-02T21:01:22.695Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c"
}
],
"title": "CVE Program Container"
},
{
"metrics": [
{
"other": {
"content": {
"id": "CVE-2023-47117",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "yes"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2025-01-08T21:11:59.859697Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2025-01-08T21:12:58.865Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.9.2post0"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is an open source data labeling tool. In all current versions of Label Studio prior to 1.9.2post0, the application allows users to insecurely set filters for filtering tasks. An attacker can construct a filter chain to filter tasks based on sensitive fields for all user accounts on the platform by exploiting Django\u0027s Object Relational Mapper (ORM). Since the results of query can be manipulated by the ORM filter, an attacker can leak these sensitive fields character by character. In addition, Label Studio had a hard coded secret key that an attacker can use to forge a session token of any user by exploiting this ORM Leak vulnerability to leak account password hashes. This vulnerability has been addressed in commit `f931d9d129` which is included in the 1.9.2post0 release. Users are advised to upgrade. There are no known workarounds for this vulnerability."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-200",
"description": "CWE-200: Exposure of Sensitive Information to an Unauthorized Actor",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2023-11-13T20:13:32.396Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c"
}
],
"source": {
"advisory": "GHSA-6hjj-gq77-j4qw",
"discovery": "UNKNOWN"
},
"title": "Object Relational Mapper Leak Vulnerability in Filtering Task in Label Studio"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-47117",
"datePublished": "2023-11-13T20:13:32.396Z",
"dateReserved": "2023-10-30T19:57:51.674Z",
"dateUpdated": "2025-01-08T21:12:58.865Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
CVE-2024-26152 (GCVE-0-2024-26152)
Vulnerability from cvelistv5
Published
2024-02-22 21:52
Modified
2024-08-14 15:32
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
Summary
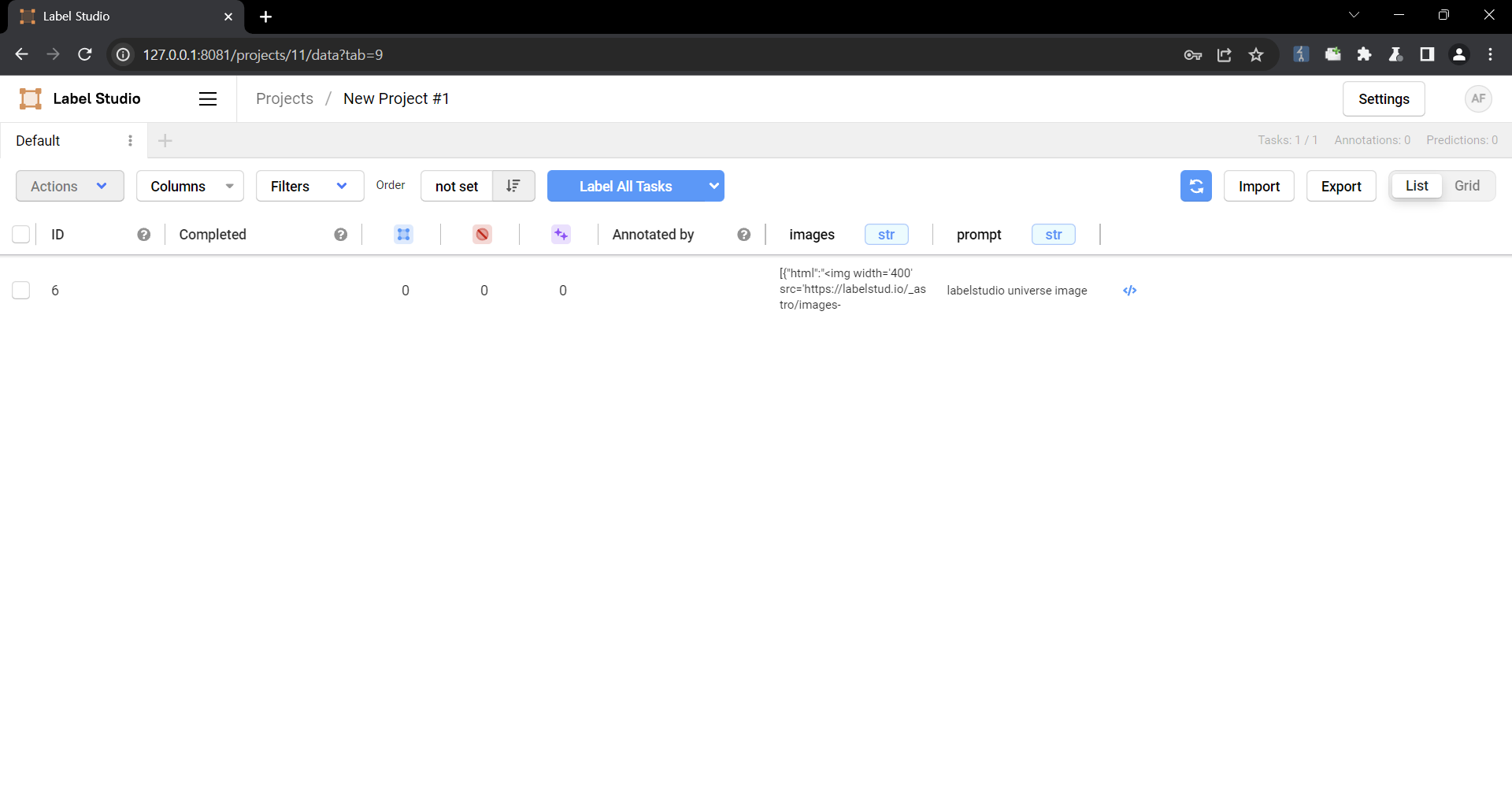
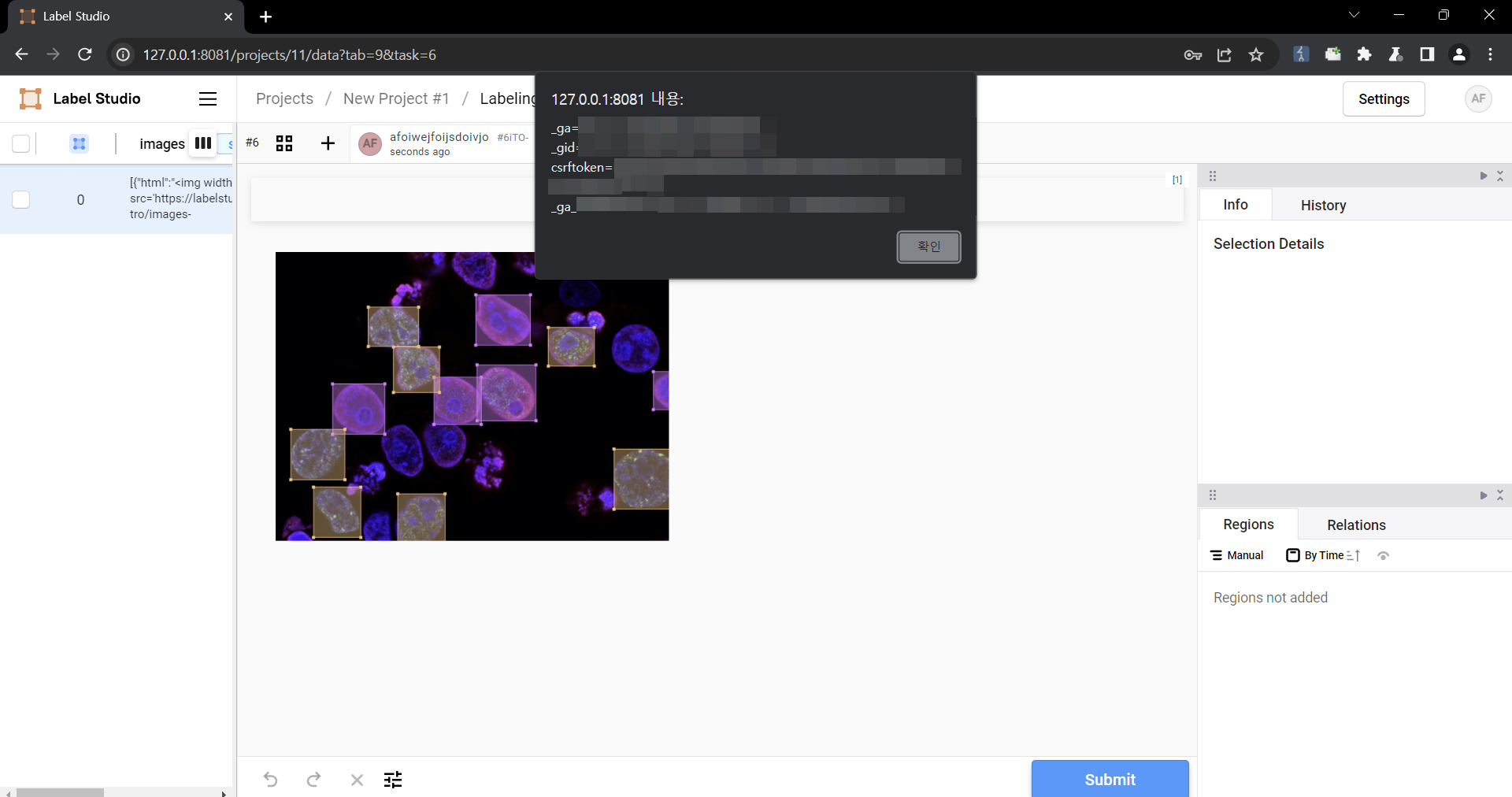
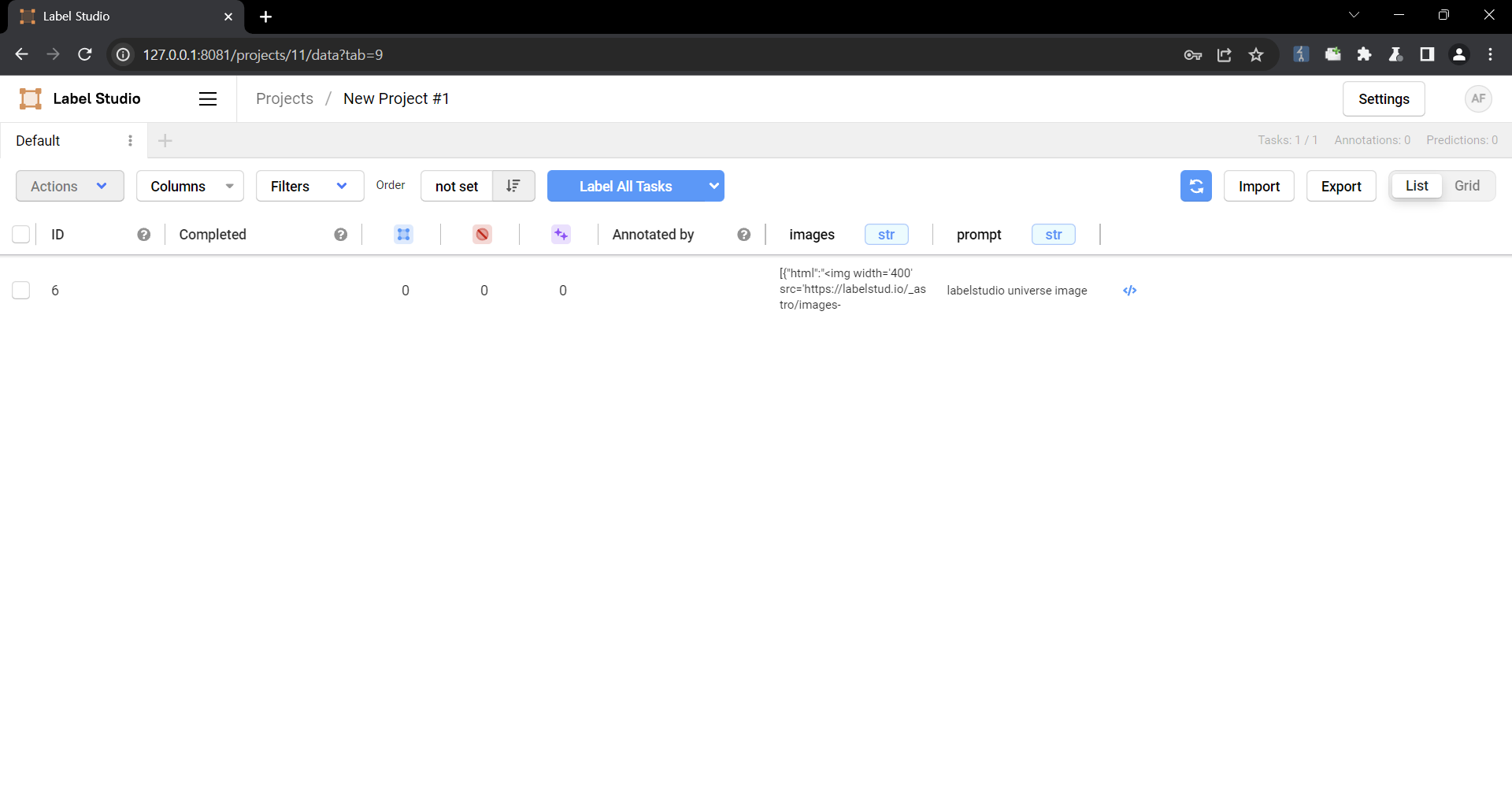
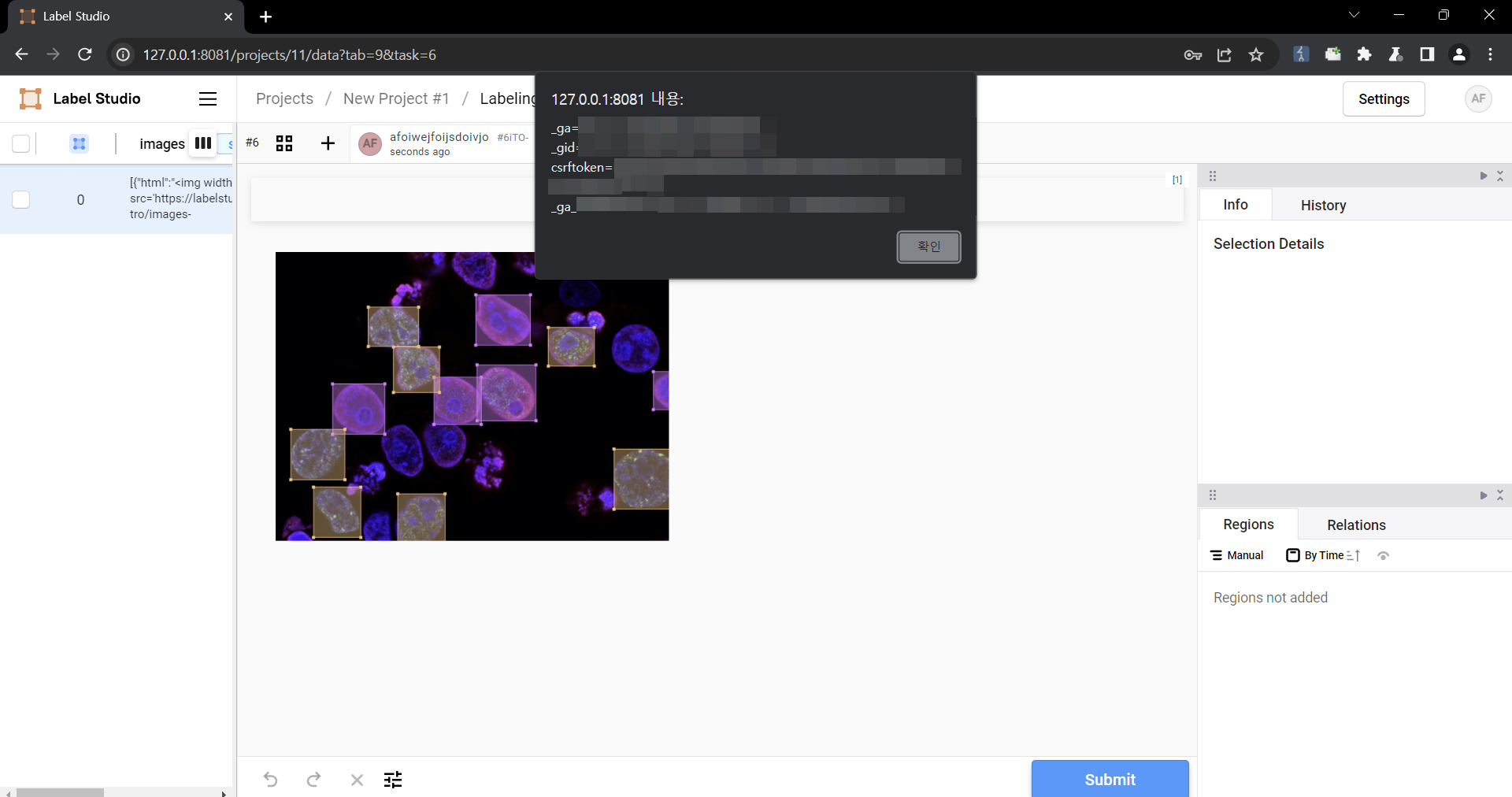
### Summary
On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.
### Details
Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1.
### PoC
1. Create a project.

2. Upload a file containing the payload using the "Upload Files" function.


The following are the contents of the files used in the PoC
```
{
"data": {
"prompt": "labelstudio universe image",
"images": [
{
"value": "id123#0",
"style": "margin: 5px",
"html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>"
}
]
}
}
```
3. Select the text-to-image generation labeling template of Ranking and scoring


4. Select a task
5. Check that the script is running
### Impact
Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
References
| ► | URL | Tags | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
||||||||||||||
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: < 1.11.0 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-01T23:59:32.696Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/5232",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"title": "CVE Program Container"
},
{
"affected": [
{
"cpes": [
"cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*"
],
"defaultStatus": "unknown",
"product": "label_studio",
"vendor": "humansignal",
"versions": [
{
"lessThan": "1.11.0",
"status": "affected",
"version": "0",
"versionType": "custom"
}
]
}
],
"metrics": [
{
"other": {
"content": {
"id": "CVE-2024-26152",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-02-23T14:32:49.819252Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-08-14T15:32:05.054Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.11.0"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "### Summary\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\n\n### Details\nNeed permission to use the \"data import\" function. This was reproduced on Label Studio 1.10.1.\n\n### PoC\n\n1. Create a project.\n\n\n2. Upload a file containing the payload using the \"Upload Files\" function.\n\n\n\nThe following are the contents of the files used in the PoC\n```\n{\n \"data\": {\n \"prompt\": \"labelstudio universe image\",\n \"images\": [\n {\n \"value\": \"id123#0\",\n \"style\": \"margin: 5px\",\n \"html\": \"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\"\n }\n ]\n }\n}\n```\n\n3. Select the text-to-image generation labeling template of Ranking and scoring\n\n\n\n4. Select a task\n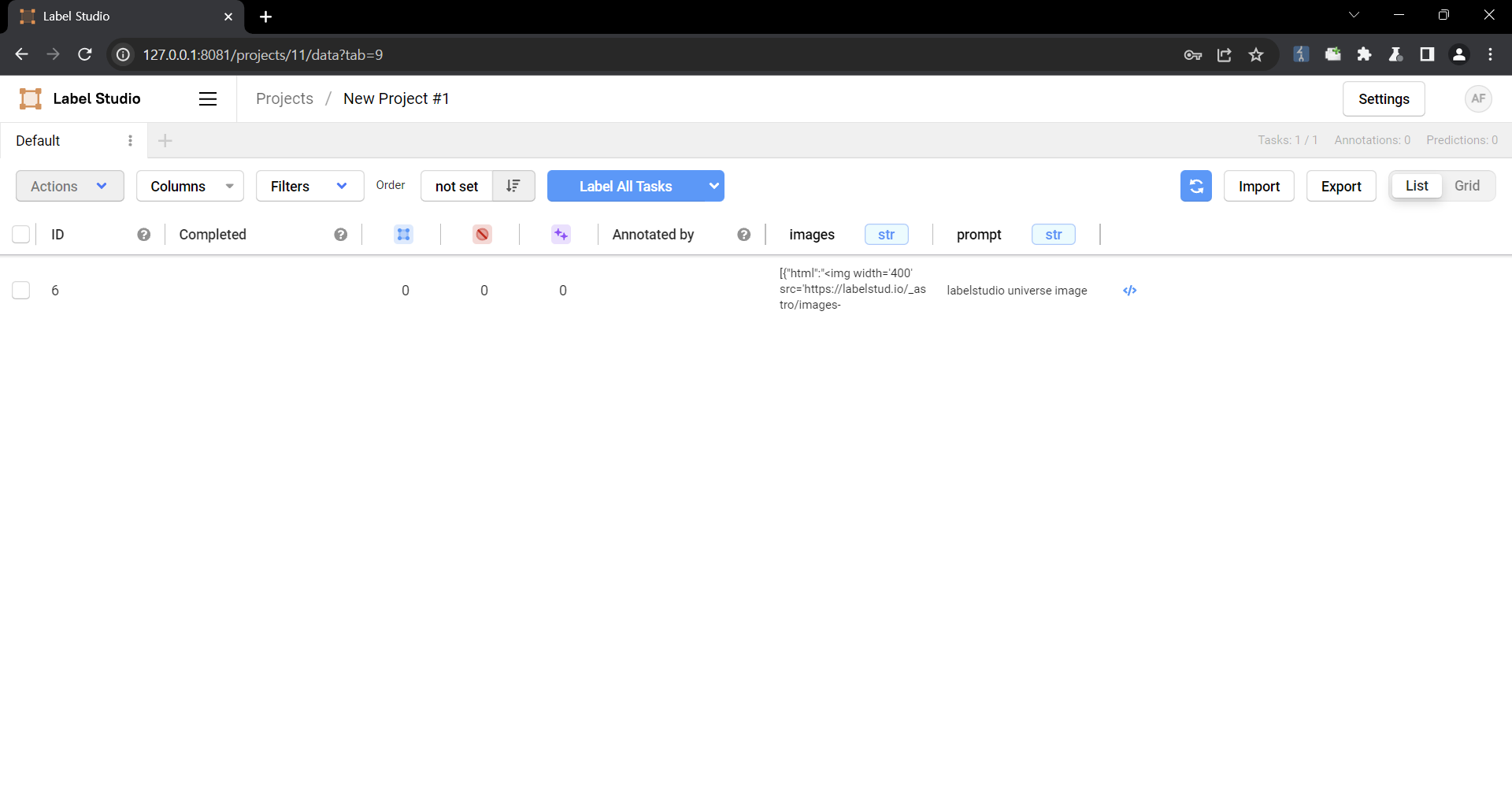\n\n5. Check that the script is running\n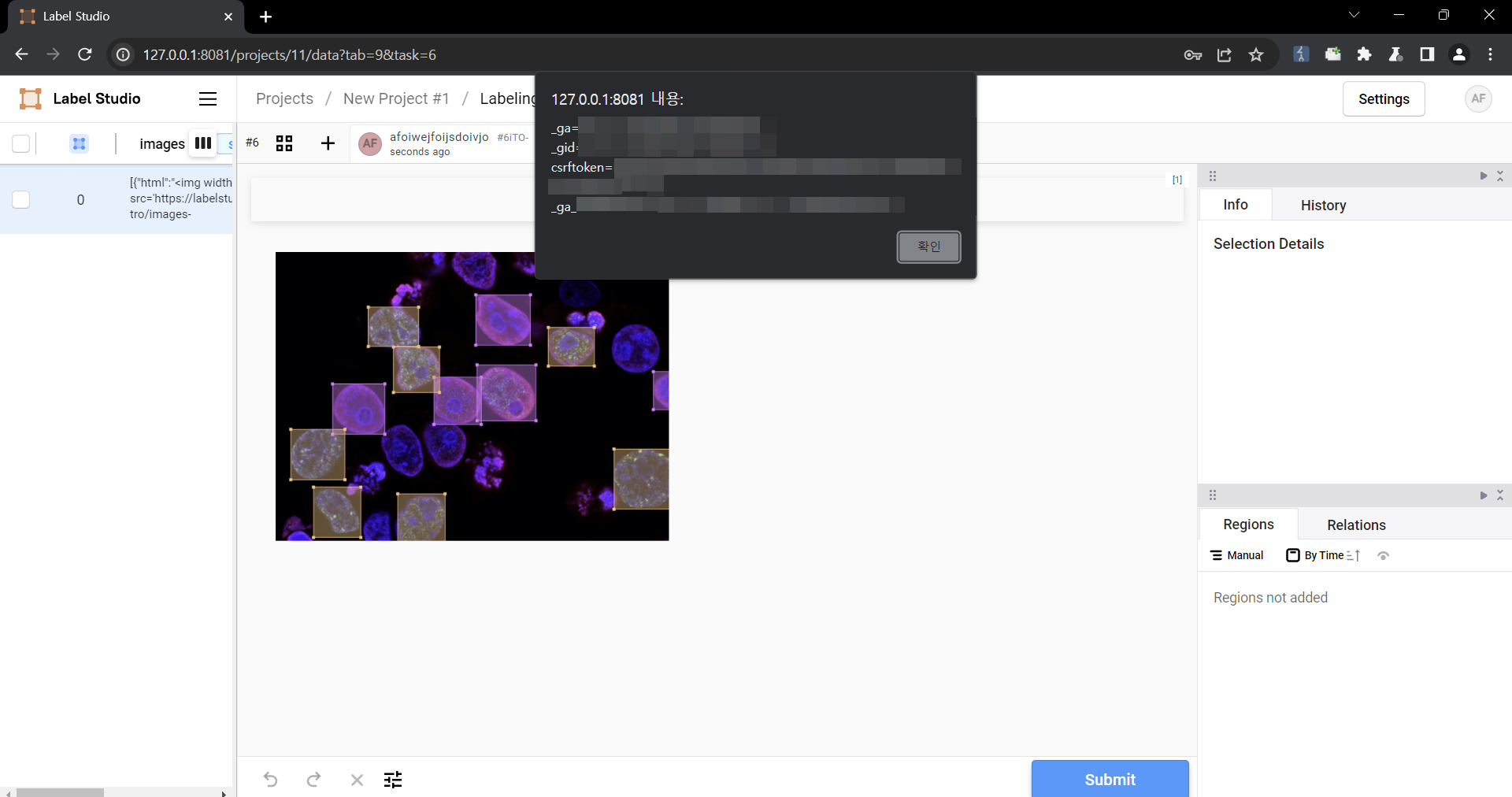\n\n### Impact\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\n"
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-79",
"description": "CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-02-22T21:52:26.193Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/5232",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"source": {
"advisory": "GHSA-6xv9-957j-qfhg",
"discovery": "UNKNOWN"
},
"title": "Label Studio vulnerable to Cross-site Scripting if `\u003cChoices\u003e` or `\u003cLabels\u003e` are used in labeling config "
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2024-26152",
"datePublished": "2024-02-22T21:52:26.193Z",
"dateReserved": "2024-02-14T17:40:03.690Z",
"dateUpdated": "2024-08-14T15:32:05.054Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
CVE-2024-23633 (GCVE-0-2024-23633)
Vulnerability from cvelistv5
Published
2024-01-23 23:15
Modified
2024-11-13 15:24
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
Summary
Label Studio, an open source data labeling tool had a remote import feature allowed users to import data from a remote web source, that was downloaded and could be viewed on the website. Prior to version 1.10.1, this feature could had been abused to download a HTML file that executed malicious JavaScript code in the context of the Label Studio website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.
`data_import/uploader.py` lines 125C5 through 146 showed that if a URL passed the server side request forgery verification checks, the contents of the file would be downloaded using the filename in the URL. The downloaded file path could then be retrieved by sending a request to `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` where `{project_id}` was the ID of the project and `{download_id}` was the ID of the downloaded file. Once the downloaded file path was retrieved by the previous API endpoint, `data_import/api.py`lines 595C1 through 616C62 demonstrated that the `Content-Type` of the response was determined by the file extension, since `mimetypes.guess_type` guesses the `Content-Type` based on the file extension. Since the `Content-Type` was determined by the file extension of the downloaded file, an attacker could import in a `.html` file that would execute JavaScript when visited.
Version 1.10.1 contains a patch for this issue. Other remediation strategies are also available. For all user provided files that are downloaded by Label Studio, set the `Content-Security-Policy: sandbox;` response header when viewed on the site. The `sandbox` directive restricts a page's actions to prevent popups, execution of plugins and scripts and enforces a `same-origin` policy. Alternatively, restrict the allowed file extensions that may be downloaded.
References
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: < 1.10.1 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-01T23:06:25.341Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r"
},
{
"name": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146"
}
],
"title": "CVE Program Container"
},
{
"metrics": [
{
"other": {
"content": {
"id": "CVE-2024-23633",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-11-13T15:23:54.398837Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-11-13T15:24:01.901Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.10.1"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Label Studio, an open source data labeling tool had a remote import feature allowed users to import data from a remote web source, that was downloaded and could be viewed on the website. Prior to version 1.10.1, this feature could had been abused to download a HTML file that executed malicious JavaScript code in the context of the Label Studio website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.\n\n`data_import/uploader.py` lines 125C5 through 146 showed that if a URL passed the server side request forgery verification checks, the contents of the file would be downloaded using the filename in the URL. The downloaded file path could then be retrieved by sending a request to `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` where `{project_id}` was the ID of the project and `{download_id}` was the ID of the downloaded file. Once the downloaded file path was retrieved by the previous API endpoint, `data_import/api.py`lines 595C1 through 616C62 demonstrated that the `Content-Type` of the response was determined by the file extension, since `mimetypes.guess_type` guesses the `Content-Type` based on the file extension. Since the `Content-Type` was determined by the file extension of the downloaded file, an attacker could import in a `.html` file that would execute JavaScript when visited.\n\nVersion 1.10.1 contains a patch for this issue. Other remediation strategies are also available. For all user provided files that are downloaded by Label Studio, set the `Content-Security-Policy: sandbox;` response header when viewed on the site. The `sandbox` directive restricts a page\u0027s actions to prevent popups, execution of plugins and scripts and enforces a `same-origin` policy. Alternatively, restrict the allowed file extensions that may be downloaded."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-79",
"description": "CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-01-23T23:15:09.044Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r"
},
{
"name": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox",
"tags": [
"x_refsource_MISC"
],
"url": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146"
}
],
"source": {
"advisory": "GHSA-fq23-g58m-799r",
"discovery": "UNKNOWN"
},
"title": " Label Studio XSS Vulnerability on Data Import"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2024-23633",
"datePublished": "2024-01-23T23:15:09.044Z",
"dateReserved": "2024-01-19T00:18:53.232Z",
"dateUpdated": "2024-11-13T15:24:01.901Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
CVE-2023-47115 (GCVE-0-2023-47115)
Vulnerability from cvelistv5
Published
2024-01-23 22:49
Modified
2025-05-30 14:18
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-79 - Improper Neutralization of Input During Web Page Generation ('Cross-site Scripting')
Summary
Label Studio is an a popular open source data labeling tool. Versions prior to 1.9.2 have a cross-site scripting (XSS) vulnerability that could be exploited when an authenticated user uploads a crafted image file for their avatar that gets rendered as a HTML file on the website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.
The file `users/functions.py` lines 18-49 show that the only verification check is that the file is an image by extracting the dimensions from the file. Label Studio serves avatar images using Django's built-in `serve` view, which is not secure for production use according to Django's documentation. The issue with the Django `serve` view is that it determines the `Content-Type` of the response by the file extension in the URL path. Therefore, an attacker can upload an image that contains malicious HTML code and name the file with a `.html` extension to be rendered as a HTML page. The only file extension validation is performed on the client-side, which can be easily bypassed.
Version 1.9.2 fixes this issue. Other remediation strategies include validating the file extension on the server side, not in client-side code; removing the use of Django's `serve` view and implement a secure controller for viewing uploaded avatar images; saving file content in the database rather than on the filesystem to mitigate against other file related vulnerabilities; and avoiding trusting user controlled inputs.
References
| ► | URL | Tags | |||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
|||||||||||||||||
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: < 1.9.2 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-02T21:01:22.795Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3"
},
{
"name": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26"
}
],
"title": "CVE Program Container"
},
{
"metrics": [
{
"other": {
"content": {
"id": "CVE-2023-47115",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2025-05-08T20:11:25.718516Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2025-05-30T14:18:15.145Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.9.2"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is an a popular open source data labeling tool. Versions prior to 1.9.2 have a cross-site scripting (XSS) vulnerability that could be exploited when an authenticated user uploads a crafted image file for their avatar that gets rendered as a HTML file on the website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.\n\nThe file `users/functions.py` lines 18-49 show that the only verification check is that the file is an image by extracting the dimensions from the file. Label Studio serves avatar images using Django\u0027s built-in `serve` view, which is not secure for production use according to Django\u0027s documentation. The issue with the Django `serve` view is that it determines the `Content-Type` of the response by the file extension in the URL path. Therefore, an attacker can upload an image that contains malicious HTML code and name the file with a `.html` extension to be rendered as a HTML page. The only file extension validation is performed on the client-side, which can be easily bypassed.\n\nVersion 1.9.2 fixes this issue. Other remediation strategies include validating the file extension on the server side, not in client-side code; removing the use of Django\u0027s `serve` view and implement a secure controller for viewing uploaded avatar images; saving file content in the database rather than on the filesystem to mitigate against other file related vulnerabilities; and avoiding trusting user controlled inputs."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:L",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-79",
"description": "CWE-79: Improper Neutralization of Input During Web Page Generation (\u0027Cross-site Scripting\u0027)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-01-23T22:49:03.958Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3"
},
{
"name": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development",
"tags": [
"x_refsource_MISC"
],
"url": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49"
},
{
"name": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26"
}
],
"source": {
"advisory": "GHSA-q68h-xwq5-mm7x",
"discovery": "UNKNOWN"
},
"title": "Label Studio XSS Vulnerability on Avatar Upload"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-47115",
"datePublished": "2024-01-23T22:49:03.958Z",
"dateReserved": "2023-10-30T19:57:51.674Z",
"dateUpdated": "2025-05-30T14:18:15.145Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
CVE-2023-47116 (GCVE-0-2023-47116)
Vulnerability from cvelistv5
Published
2024-01-31 16:21
Modified
2025-06-17 21:29
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-918 - Server-Side Request Forgery (SSRF)
Summary
Label Studio is a popular open source data labeling tool. The vulnerability affects all versions of Label Studio prior to 1.11.0 and was tested on version 1.8.2. Label Studio's SSRF protections that can be enabled by setting the `SSRF_PROTECTION_ENABLED` environment variable can be bypassed to access internal web servers. This is because the current SSRF validation is done by executing a single DNS lookup to verify that the IP address is not in an excluded subnet range. This protection can be bypassed by either using HTTP redirection or performing a DNS rebinding attack.
References
| ► | URL | Tags |
|---|---|---|
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: < 1.11.0 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-02T21:01:22.711Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"title": "CVE Program Container"
},
{
"metrics": [
{
"other": {
"content": {
"id": "CVE-2023-47116",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "no"
},
{
"Technical Impact": "partial"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-01-31T20:33:12.634033Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2025-06-17T21:29:19.276Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c 1.11.0"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is a popular open source data labeling tool. The vulnerability affects all versions of Label Studio prior to 1.11.0 and was tested on version 1.8.2. Label Studio\u0027s SSRF protections that can be enabled by setting the `SSRF_PROTECTION_ENABLED` environment variable can be bypassed to access internal web servers. This is because the current SSRF validation is done by executing a single DNS lookup to verify that the IP address is not in an excluded subnet range. This protection can be bypassed by either using HTTP redirection or performing a DNS rebinding attack."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-918",
"description": "CWE-918: Server-Side Request Forgery (SSRF)",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2024-01-31T16:21:50.793Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
}
],
"source": {
"advisory": "GHSA-p59w-9gqw-wj8r",
"discovery": "UNKNOWN"
},
"title": "Label Studio SSRF on Import Bypassing `SSRF_PROTECTION_ENABLED` Protections"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-47116",
"datePublished": "2024-01-31T16:21:50.793Z",
"dateReserved": "2023-10-30T19:57:51.674Z",
"dateUpdated": "2025-06-17T21:29:19.276Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
CVE-2023-43791 (GCVE-0-2023-43791)
Vulnerability from cvelistv5
Published
2023-11-09 14:42
Modified
2024-09-03 18:46
Severity ?
VLAI Severity ?
EPSS score ?
CWE
- CWE-200 - Exposure of Sensitive Information to an Unauthorized Actor
Summary
Label Studio is a multi-type data labeling and annotation tool with standardized output format. There is a vulnerability that can be chained within the ORM Leak vulnerability to impersonate any account on Label Studio. An attacker could exploit these vulnerabilities to escalate their privileges from a low privilege user to a Django Super Administrator user. The vulnerability was found to affect versions before `1.8.2`, where a patch was introduced.
References
| ► | URL | Tags | ||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
|
||||||||||||||
Impacted products
| Vendor | Product | Version | ||
|---|---|---|---|---|
| HumanSignal | label-studio |
Version: <= 1.8.1 |
{
"containers": {
"adp": [
{
"providerMetadata": {
"dateUpdated": "2024-08-02T19:52:11.411Z",
"orgId": "af854a3a-2127-422b-91ae-364da2661108",
"shortName": "CVE"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m",
"tags": [
"x_refsource_CONFIRM",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/4690",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/pull/4690"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2",
"tags": [
"x_refsource_MISC",
"x_transferred"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2"
}
],
"title": "CVE Program Container"
},
{
"metrics": [
{
"other": {
"content": {
"id": "CVE-2023-43791",
"options": [
{
"Exploitation": "poc"
},
{
"Automatable": "yes"
},
{
"Technical Impact": "total"
}
],
"role": "CISA Coordinator",
"timestamp": "2024-09-03T18:43:34.308098Z",
"version": "2.0.3"
},
"type": "ssvc"
}
}
],
"providerMetadata": {
"dateUpdated": "2024-09-03T18:46:40.834Z",
"orgId": "134c704f-9b21-4f2e-91b3-4a467353bcc0",
"shortName": "CISA-ADP"
},
"title": "CISA ADP Vulnrichment"
}
],
"cna": {
"affected": [
{
"product": "label-studio",
"vendor": "HumanSignal",
"versions": [
{
"status": "affected",
"version": "\u003c= 1.8.1"
}
]
}
],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is a multi-type data labeling and annotation tool with standardized output format. There is a vulnerability that can be chained within the ORM Leak vulnerability to impersonate any account on Label Studio. An attacker could exploit these vulnerabilities to escalate their privileges from a low privilege user to a Django Super Administrator user. The vulnerability was found to affect versions before `1.8.2`, where a patch was introduced."
}
],
"metrics": [
{
"cvssV3_1": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
}
}
],
"problemTypes": [
{
"descriptions": [
{
"cweId": "CWE-200",
"description": "CWE-200: Exposure of Sensitive Information to an Unauthorized Actor",
"lang": "en",
"type": "CWE"
}
]
}
],
"providerMetadata": {
"dateUpdated": "2023-11-09T14:42:40.750Z",
"orgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"shortName": "GitHub_M"
},
"references": [
{
"name": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m",
"tags": [
"x_refsource_CONFIRM"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m"
},
{
"name": "https://github.com/HumanSignal/label-studio/pull/4690",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/pull/4690"
},
{
"name": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b"
},
{
"name": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2",
"tags": [
"x_refsource_MISC"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2"
}
],
"source": {
"advisory": "GHSA-f475-x83m-rx5m",
"discovery": "UNKNOWN"
},
"title": "Label Studio has Hardcoded Django `SECRET_KEY` that can be Abused to Forge Session Tokens"
}
},
"cveMetadata": {
"assignerOrgId": "a0819718-46f1-4df5-94e2-005712e83aaa",
"assignerShortName": "GitHub_M",
"cveId": "CVE-2023-43791",
"datePublished": "2023-11-09T14:42:40.750Z",
"dateReserved": "2023-09-22T14:51:42.339Z",
"dateUpdated": "2024-09-03T18:46:40.834Z",
"state": "PUBLISHED"
},
"dataType": "CVE_RECORD",
"dataVersion": "5.1"
}
Vulnerability from fkie_nvd
Published
2023-11-13 21:15
Modified
2024-11-21 08:29
Severity ?
7.5 (High) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
7.5 (High) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
7.5 (High) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Summary
Label Studio is an open source data labeling tool. In all current versions of Label Studio prior to 1.9.2post0, the application allows users to insecurely set filters for filtering tasks. An attacker can construct a filter chain to filter tasks based on sensitive fields for all user accounts on the platform by exploiting Django's Object Relational Mapper (ORM). Since the results of query can be manipulated by the ORM filter, an attacker can leak these sensitive fields character by character. In addition, Label Studio had a hard coded secret key that an attacker can use to forge a session token of any user by exploiting this ORM Leak vulnerability to leak account password hashes. This vulnerability has been addressed in commit `f931d9d129` which is included in the 1.9.2post0 release. Users are advised to upgrade. There are no known workarounds for this vulnerability.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw | Exploit, Mitigation, Vendor Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw | Exploit, Mitigation, Vendor Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * | |
| humansignal | label_studio | 1.9.2 |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "326DCEFD-7346-4651-80AD-728FE9E4BD87",
"versionEndExcluding": "1.9.2",
"vulnerable": true
},
{
"criteria": "cpe:2.3:a:humansignal:label_studio:1.9.2:-:*:*:*:*:*:*",
"matchCriteriaId": "6ED24348-4388-489F-A77F-51B3CE76714D",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is an open source data labeling tool. In all current versions of Label Studio prior to 1.9.2post0, the application allows users to insecurely set filters for filtering tasks. An attacker can construct a filter chain to filter tasks based on sensitive fields for all user accounts on the platform by exploiting Django\u0027s Object Relational Mapper (ORM). Since the results of query can be manipulated by the ORM filter, an attacker can leak these sensitive fields character by character. In addition, Label Studio had a hard coded secret key that an attacker can use to forge a session token of any user by exploiting this ORM Leak vulnerability to leak account password hashes. This vulnerability has been addressed in commit `f931d9d129` which is included in the 1.9.2post0 release. Users are advised to upgrade. There are no known workarounds for this vulnerability."
},
{
"lang": "es",
"value": "Label Studio es una herramienta de etiquetado de datos de c\u00f3digo abierto. En todas las versiones actuales de Label Studio anteriores a la 1.9.2post0, la aplicaci\u00f3n permite a los usuarios configurar filtros de forma insegura para tareas de filtrado. Un atacante puede construir una cadena de filtros para filtrar tareas basadas en campos confidenciales para todas las cuentas de usuario en la plataforma explotando el Object Relational Mapper (ORM) de Django. Dado que los resultados de la consulta pueden ser manipulados por el filtro ORM, un atacante puede filtrar estos campos confidenciales car\u00e1cter por car\u00e1cter. Adem\u00e1s, Label Studio ten\u00eda una clave secreta codificada que un atacante puede usar para falsificar un token de sesi\u00f3n de cualquier usuario explotando esta vulnerabilidad de fuga de ORM para filtrar hashes de contrase\u00f1as de cuentas. Esta vulnerabilidad se solucion\u00f3 en el commit `f931d9d129` que se incluye en la versi\u00f3n 1.9.2post0. Se recomienda a los usuarios que actualicen. No se conocen workarounds para esta vulnerabilidad."
}
],
"id": "CVE-2023-47117",
"lastModified": "2024-11-21T08:29:48.757",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 7.5,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 3.6,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2023-11-13T21:15:08.317",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Mitigation",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/f931d9d129002f54a495995774ce7384174cef5c"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Mitigation",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6hjj-gq77-j4qw"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-200"
}
],
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"description": [
{
"lang": "en",
"value": "NVD-CWE-noinfo"
}
],
"source": "nvd@nist.gov",
"type": "Primary"
}
]
}
Vulnerability from fkie_nvd
Published
2023-11-09 15:15
Modified
2024-11-21 08:24
Severity ?
9.8 (Critical) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
8.8 (High) - CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
8.8 (High) - CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H
Summary
Label Studio is a multi-type data labeling and annotation tool with standardized output format. There is a vulnerability that can be chained within the ORM Leak vulnerability to impersonate any account on Label Studio. An attacker could exploit these vulnerabilities to escalate their privileges from a low privilege user to a Django Super Administrator user. The vulnerability was found to affect versions before `1.8.2`, where a patch was introduced.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/pull/4690 | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/releases/tag/1.8.2 | Release Notes | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m | Exploit, Vendor Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/pull/4690 | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/releases/tag/1.8.2 | Release Notes | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m | Exploit, Vendor Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "ACEFE38F-DAA5-4450-9527-0669A8790ADC",
"versionEndExcluding": "1.8.2",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is a multi-type data labeling and annotation tool with standardized output format. There is a vulnerability that can be chained within the ORM Leak vulnerability to impersonate any account on Label Studio. An attacker could exploit these vulnerabilities to escalate their privileges from a low privilege user to a Django Super Administrator user. The vulnerability was found to affect versions before `1.8.2`, where a patch was introduced."
},
{
"lang": "es",
"value": "Label Studio es una herramienta de anotaci\u00f3n y etiquetado de datos de varios tipos con formato de salida estandarizado. Existe una vulnerabilidad que se puede encadenar dentro de la vulnerabilidad ORM Leak para hacerse pasar por cualquier cuenta en Label Studio. Un atacante podr\u00eda aprovechar estas vulnerabilidades para escalar sus privilegios de un usuario con permisos bajos a un usuario s\u00faper administrador de Django. Se descubri\u00f3 que la vulnerabilidad afectaba a versiones anteriores a la \"1.8.2\", donde se introdujo un parche."
}
],
"id": "CVE-2023-43791",
"lastModified": "2024-11-21T08:24:47.447",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 9.8,
"baseSeverity": "CRITICAL",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 5.9,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "HIGH",
"baseScore": 8.8,
"baseSeverity": "HIGH",
"confidentialityImpact": "HIGH",
"integrityImpact": "HIGH",
"privilegesRequired": "LOW",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 5.9,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2023-11-09T15:15:08.743",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/pull/4690"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/3d06c5131c15600621e08b06f07d976887cde81b"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/pull/4690"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.8.2"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-f475-x83m-rx5m"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-200"
}
],
"source": "security-advisories@github.com",
"type": "Primary"
}
]
}
Vulnerability from fkie_nvd
Published
2024-01-31 17:15
Modified
2024-11-21 08:29
Severity ?
5.3 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N
5.3 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N
5.3 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N
Summary
Label Studio is a popular open source data labeling tool. The vulnerability affects all versions of Label Studio prior to 1.11.0 and was tested on version 1.8.2. Label Studio's SSRF protections that can be enabled by setting the `SSRF_PROTECTION_ENABLED` environment variable can be bypassed to access internal web servers. This is because the current SSRF validation is done by executing a single DNS lookup to verify that the IP address is not in an excluded subnet range. This protection can be bypassed by either using HTTP redirection or performing a DNS rebinding attack.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64 | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/releases/tag/1.11.0 | Release Notes | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r | Exploit, Third Party Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64 | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/releases/tag/1.11.0 | Release Notes | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r | Exploit, Third Party Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "27567917-A7FB-4767-B9F6-6C8D422D62E7",
"versionEndExcluding": "1.11.0",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is a popular open source data labeling tool. The vulnerability affects all versions of Label Studio prior to 1.11.0 and was tested on version 1.8.2. Label Studio\u0027s SSRF protections that can be enabled by setting the `SSRF_PROTECTION_ENABLED` environment variable can be bypassed to access internal web servers. This is because the current SSRF validation is done by executing a single DNS lookup to verify that the IP address is not in an excluded subnet range. This protection can be bypassed by either using HTTP redirection or performing a DNS rebinding attack."
},
{
"lang": "es",
"value": "Label Studio es una popular herramienta de etiquetado de datos de c\u00f3digo abierto. La vulnerabilidad afecta a todas las versiones de Label Studio anteriores a la 1.11.0 y se prob\u00f3 en la versi\u00f3n 1.8.2. Las protecciones SSRF de Label Studio que se pueden habilitar configurando la variable de entorno `SSRF_PROTECTION_ENABLED` se pueden omitir para acceder a los servidores web internos. Esto se debe a que la validaci\u00f3n SSRF actual se realiza ejecutando una \u00fanica b\u00fasqueda de DNS para verificar que la direcci\u00f3n IP no est\u00e9 en un rango de subred excluido. Esta protecci\u00f3n se puede omitir utilizando la redirecci\u00f3n HTTP o realizando un ataque de vinculaci\u00f3n de DNS."
}
],
"id": "CVE-2023-47116",
"lastModified": "2024-11-21T08:29:48.630",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 1.4,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.3,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "UNCHANGED",
"userInteraction": "NONE",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 3.9,
"impactScore": 1.4,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2024-01-31T17:15:13.370",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/55dd6af4716b92f2bb213fe461d1ffbc380c6a64"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-p59w-9gqw-wj8r"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-918"
}
],
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"description": [
{
"lang": "en",
"value": "CWE-918"
}
],
"source": "nvd@nist.gov",
"type": "Primary"
}
]
}
Vulnerability from fkie_nvd
Published
2024-02-22 22:15
Modified
2025-05-16 14:18
Severity ?
4.7 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N
6.1 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
6.1 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Summary
### Summary
On all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.
### Details
Need permission to use the "data import" function. This was reproduced on Label Studio 1.10.1.
### PoC
1. Create a project.

2. Upload a file containing the payload using the "Upload Files" function.


The following are the contents of the files used in the PoC
```
{
"data": {
"prompt": "labelstudio universe image",
"images": [
{
"value": "id123#0",
"style": "margin: 5px",
"html": "<img width='400' src='https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif' onload=alert(document.cookie)>"
}
]
}
}
```
3. Select the text-to-image generation labeling template of Ranking and scoring


4. Select a task
5. Check that the script is running
### Impact
Malicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8 | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/pull/5232 | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/releases/tag/1.11.0 | Release Notes | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg | Exploit, Vendor Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8 | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/pull/5232 | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/releases/tag/1.11.0 | Release Notes | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg | Exploit, Vendor Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "27567917-A7FB-4767-B9F6-6C8D422D62E7",
"versionEndExcluding": "1.11.0",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "### Summary\nOn all Label Studio versions prior to 1.11.0, data imported via file upload feature is not properly sanitized prior to being rendered within a [`Choices`](https://labelstud.io/tags/choices) or [`Labels`](https://labelstud.io/tags/labels) tag, resulting in an XSS vulnerability.\n\n### Details\nNeed permission to use the \"data import\" function. This was reproduced on Label Studio 1.10.1.\n\n### PoC\n\n1. Create a project.\n\n\n2. Upload a file containing the payload using the \"Upload Files\" function.\n\n\n\nThe following are the contents of the files used in the PoC\n```\n{\n \"data\": {\n \"prompt\": \"labelstudio universe image\",\n \"images\": [\n {\n \"value\": \"id123#0\",\n \"style\": \"margin: 5px\",\n \"html\": \"\u003cimg width=\u0027400\u0027 src=\u0027https://labelstud.io/_astro/images-tab.64279c16_ZaBSvC.avif\u0027 onload=alert(document.cookie)\u003e\"\n }\n ]\n }\n}\n```\n\n3. Select the text-to-image generation labeling template of Ranking and scoring\n\n\n\n4. Select a task\n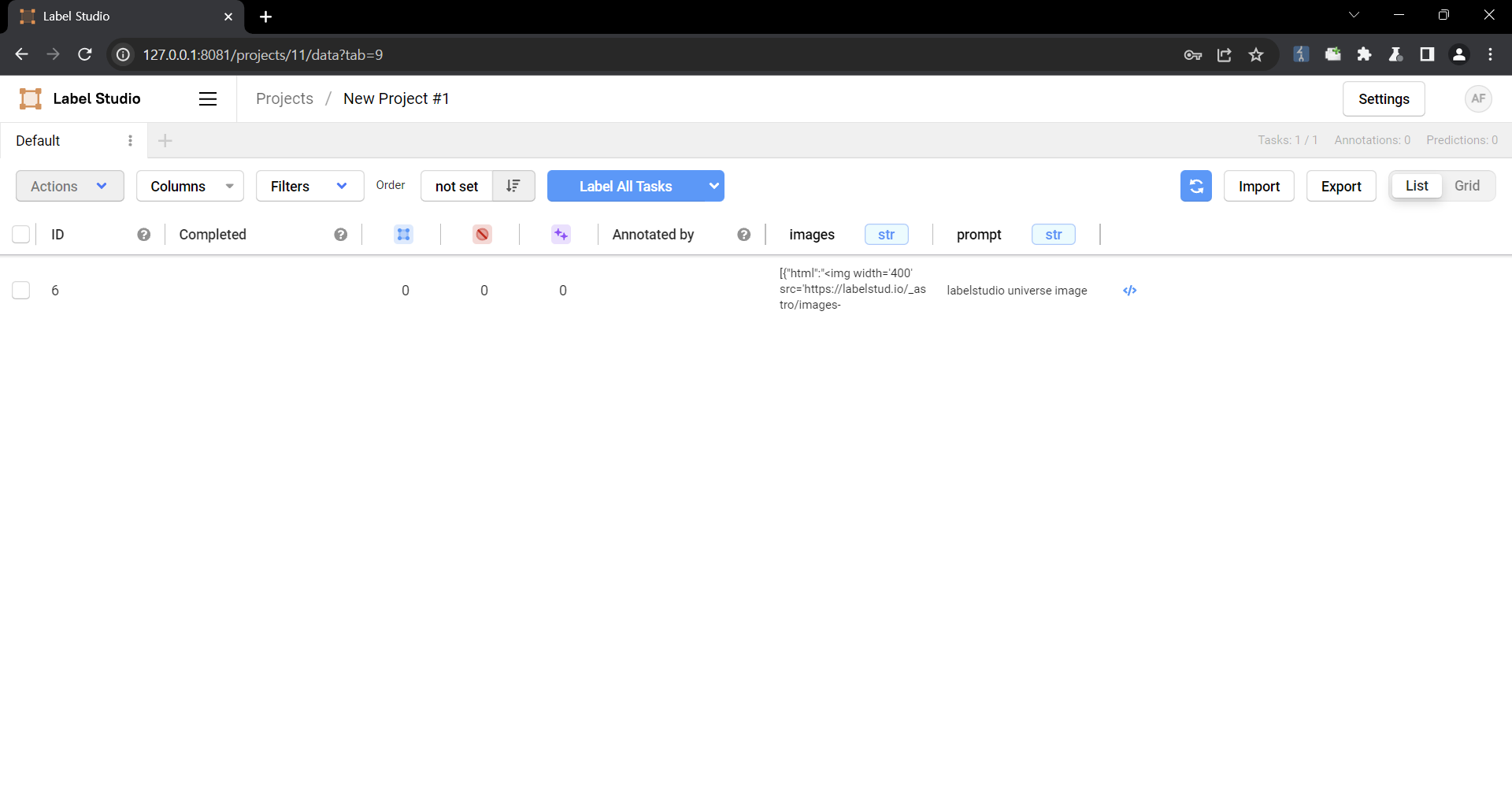\n\n5. Check that the script is running\n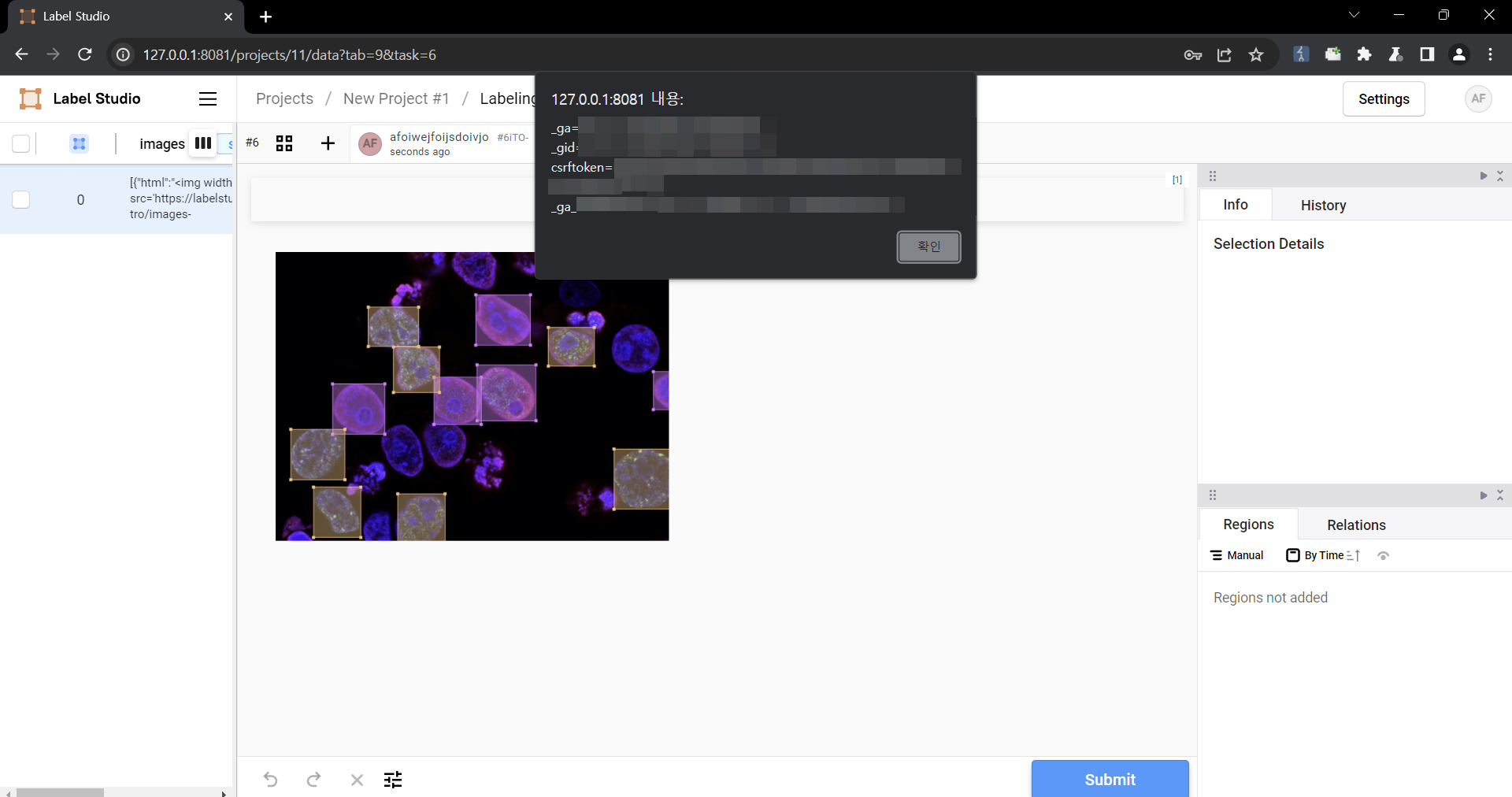\n\n### Impact\nMalicious scripts can be injected into the code, and when linked with vulnerabilities such as CSRF, it can cause even greater damage. In particular, It can become a source of further attacks, especially when linked to social engineering.\n"
},
{
"lang": "es",
"value": "### Resumen En todas las versiones de Label Studio anteriores a la 1.11.0, los datos importados mediante la funci\u00f3n de carga de archivos no se desinfectan adecuadamente antes de procesarse dentro de [`Choices`](https://labelstud.io/tags/choices) o [`Labels`](https://labelstud.io/tags/labels), lo que genera una vulnerabilidad XSS. ### Detalles Necesita permiso para utilizar la funci\u00f3n \"importaci\u00f3n de datos\". Esto fue reproducido en Label Studio 1.10.1. ### PoC 1. Cree un proyecto.  2. Cargue un archivo que contenga la carga \u00fatil usando la funci\u00f3n \"Cargar archivos\" .   Los siguientes son los contenidos de los archivos utilizados en el PoC ``` { \"data\": { \" Prompt\": \"imagen del universo de labelstudio\", \"images\": [ { \"value\": \"id123#0\", \"style\": \"margin: 5px\", \"html\": \"\" } ] } } ``` 3. Seleccione la plantilla de etiquetado de generaci\u00f3n de texto a imagen de Clasificaci\u00f3n y puntuaci\u00f3n 4. \u00a1Seleccione una tarea! [4 Seleccione una tarea](https://github.com/HumanSignal/label-studio/assets/3943358/71856b7a-2b1f-44ea-99ab-fc48bc20caa7) 5. \u00a1Compruebe que el script se est\u00e9 ejecutando! [5 Compruebe que el script se est\u00e9 ejecutando](https://github.com/ HumanSignal/label-studio/assets/3943358/e396ae7b-a591-4db7-afe9-5bab30b48cb9) ### Impacto Se pueden inyectar scripts maliciosos en el c\u00f3digo y, cuando se vinculan con vulnerabilidades como CSRF, pueden causar un da\u00f1o a\u00fan mayor. En particular, puede convertirse en una fuente de nuevos ataques, especialmente cuando se vincula a la ingenier\u00eda social."
}
],
"id": "CVE-2024-26152",
"lastModified": "2025-05-16T14:18:25.530",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 1.4,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 2.7,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2024-02-22T22:15:47.310",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"source": "security-advisories@github.com",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/5df9ae3828b98652e9fa290a19f4deedf51ef6c8"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/pull/5232"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Release Notes"
],
"url": "https://github.com/HumanSignal/label-studio/releases/tag/1.11.0"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Vendor Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-6xv9-957j-qfhg"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Analyzed",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "nvd@nist.gov",
"type": "Primary"
}
]
}
Vulnerability from fkie_nvd
Published
2024-01-23 23:15
Modified
2024-11-21 08:29
Severity ?
7.1 (High) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:L
5.4 (Medium) - CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N
5.4 (Medium) - CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N
Summary
Label Studio is an a popular open source data labeling tool. Versions prior to 1.9.2 have a cross-site scripting (XSS) vulnerability that could be exploited when an authenticated user uploads a crafted image file for their avatar that gets rendered as a HTML file on the website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.
The file `users/functions.py` lines 18-49 show that the only verification check is that the file is an image by extracting the dimensions from the file. Label Studio serves avatar images using Django's built-in `serve` view, which is not secure for production use according to Django's documentation. The issue with the Django `serve` view is that it determines the `Content-Type` of the response by the file extension in the URL path. Therefore, an attacker can upload an image that contains malicious HTML code and name the file with a `.html` extension to be rendered as a HTML page. The only file extension validation is performed on the client-side, which can be easily bypassed.
Version 1.9.2 fixes this issue. Other remediation strategies include validating the file extension on the server side, not in client-side code; removing the use of Django's `serve` view and implement a secure controller for viewing uploaded avatar images; saving file content in the database rather than on the filesystem to mitigate against other file related vulnerabilities; and avoiding trusting user controlled inputs.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development | Not Applicable | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49 | Product | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26 | Product | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3 | Patch | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x | Exploit, Third Party Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development | Not Applicable | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49 | Product | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26 | Product | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3 | Patch | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x | Exploit, Third Party Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "326DCEFD-7346-4651-80AD-728FE9E4BD87",
"versionEndExcluding": "1.9.2",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "Label Studio is an a popular open source data labeling tool. Versions prior to 1.9.2 have a cross-site scripting (XSS) vulnerability that could be exploited when an authenticated user uploads a crafted image file for their avatar that gets rendered as a HTML file on the website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.\n\nThe file `users/functions.py` lines 18-49 show that the only verification check is that the file is an image by extracting the dimensions from the file. Label Studio serves avatar images using Django\u0027s built-in `serve` view, which is not secure for production use according to Django\u0027s documentation. The issue with the Django `serve` view is that it determines the `Content-Type` of the response by the file extension in the URL path. Therefore, an attacker can upload an image that contains malicious HTML code and name the file with a `.html` extension to be rendered as a HTML page. The only file extension validation is performed on the client-side, which can be easily bypassed.\n\nVersion 1.9.2 fixes this issue. Other remediation strategies include validating the file extension on the server side, not in client-side code; removing the use of Django\u0027s `serve` view and implement a secure controller for viewing uploaded avatar images; saving file content in the database rather than on the filesystem to mitigate against other file related vulnerabilities; and avoiding trusting user controlled inputs."
},
{
"lang": "es",
"value": "Label Studio es una popular herramienta de etiquetado de datos de c\u00f3digo abierto. Las versiones anteriores a la 1.9.2 tienen una vulnerabilidad de cross-site scripting (XSS) que podr\u00eda explotarse cuando un usuario autenticado carga un archivo de imagen manipulado para su avatar que se representa como un archivo HTML en el sitio web. La ejecuci\u00f3n de JavaScript arbitrario podr\u00eda provocar que un atacante realice acciones maliciosas en los usuarios de Label Studio si visitan la imagen de avatar creada. Por ejemplo, un atacante puede crear un payload de JavaScript que agregue un nuevo usuario de Superadministrador de Django si un administrador de Django visita la imagen. Las l\u00edneas 18-49 del archivo `users/functions.py` muestran que la \u00fanica verificaci\u00f3n de verificaci\u00f3n es que el archivo es una imagen extrayendo las dimensiones del archivo. Label Studio sirve im\u00e1genes de avatar utilizando la vista \"servir\" incorporada de Django, que no es segura para uso en producci\u00f3n seg\u00fan la documentaci\u00f3n de Django. El problema con la vista `serve` de Django es que determina el `Tipo de contenido` de la respuesta por la extensi\u00f3n del archivo en la ruta URL. Por lo tanto, un atacante puede cargar una imagen que contenga c\u00f3digo HTML malicioso y nombrar el archivo con una extensi\u00f3n \".html\" para que se represente como una p\u00e1gina HTML. La \u00fanica validaci\u00f3n de la extensi\u00f3n de archivo se realiza en el lado del cliente, lo que se puede omitir f\u00e1cilmente. La versi\u00f3n 1.9.2 soluciona este problema. Otras estrategias de correcci\u00f3n incluyen validar la extensi\u00f3n del archivo en el lado del servidor, no en el c\u00f3digo del lado del cliente; eliminar el uso de la vista `serve` de Django e implementar un controlador seguro para ver las im\u00e1genes de avatar cargadas; guardar el contenido del archivo en la base de datos en lugar de en el sistema de archivos para mitigar otras vulnerabilidades relacionadas con los archivos; y evitar confiar en las entradas controladas por el usuario."
}
],
"id": "CVE-2023-47115",
"lastModified": "2024-11-21T08:29:48.500",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "LOW",
"baseScore": 7.1,
"baseSeverity": "HIGH",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:L",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 3.7,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 5.4,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "LOW",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:L/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.3,
"impactScore": 2.7,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2024-01-23T23:15:08.100",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Not Applicable"
],
"url": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development"
},
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49"
},
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26"
},
{
"source": "security-advisories@github.com",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3"
},
{
"source": "security-advisories@github.com",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Not Applicable"
],
"url": "https://docs.djangoproject.com/en/4.2/ref/views/#serving-files-in-development"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/functions.py#L18-L49"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.8.2/label_studio/users/urls.py#L25-L26"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Patch"
],
"url": "https://github.com/HumanSignal/label-studio/commit/a7a71e594f32ec4af8f3f800d5ccb8662e275da3"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Exploit",
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-q68h-xwq5-mm7x"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "nvd@nist.gov",
"type": "Primary"
}
]
}
Vulnerability from fkie_nvd
Published
2024-01-24 00:15
Modified
2024-11-21 08:58
Severity ?
4.7 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N
6.1 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
6.1 (Medium) - CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N
Summary
Label Studio, an open source data labeling tool had a remote import feature allowed users to import data from a remote web source, that was downloaded and could be viewed on the website. Prior to version 1.10.1, this feature could had been abused to download a HTML file that executed malicious JavaScript code in the context of the Label Studio website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.
`data_import/uploader.py` lines 125C5 through 146 showed that if a URL passed the server side request forgery verification checks, the contents of the file would be downloaded using the filename in the URL. The downloaded file path could then be retrieved by sending a request to `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` where `{project_id}` was the ID of the project and `{download_id}` was the ID of the downloaded file. Once the downloaded file path was retrieved by the previous API endpoint, `data_import/api.py`lines 595C1 through 616C62 demonstrated that the `Content-Type` of the response was determined by the file extension, since `mimetypes.guess_type` guesses the `Content-Type` based on the file extension. Since the `Content-Type` was determined by the file extension of the downloaded file, an attacker could import in a `.html` file that would execute JavaScript when visited.
Version 1.10.1 contains a patch for this issue. Other remediation strategies are also available. For all user provided files that are downloaded by Label Studio, set the `Content-Security-Policy: sandbox;` response header when viewed on the site. The `sandbox` directive restricts a page's actions to prevent popups, execution of plugins and scripts and enforces a `same-origin` policy. Alternatively, restrict the allowed file extensions that may be downloaded.
References
| ▶ | URL | Tags | |
|---|---|---|---|
| security-advisories@github.com | https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox | Not Applicable | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62 | Product | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146 | Product | |
| security-advisories@github.com | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r | Third Party Advisory | |
| af854a3a-2127-422b-91ae-364da2661108 | https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox | Not Applicable | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62 | Product | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146 | Product | |
| af854a3a-2127-422b-91ae-364da2661108 | https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r | Third Party Advisory |
Impacted products
| Vendor | Product | Version | |
|---|---|---|---|
| humansignal | label_studio | * |
{
"configurations": [
{
"nodes": [
{
"cpeMatch": [
{
"criteria": "cpe:2.3:a:humansignal:label_studio:*:*:*:*:*:*:*:*",
"matchCriteriaId": "0851F09C-7B83-47B1-8217-1394F68D0B13",
"versionEndExcluding": "1.10.1",
"vulnerable": true
}
],
"negate": false,
"operator": "OR"
}
]
}
],
"cveTags": [],
"descriptions": [
{
"lang": "en",
"value": "Label Studio, an open source data labeling tool had a remote import feature allowed users to import data from a remote web source, that was downloaded and could be viewed on the website. Prior to version 1.10.1, this feature could had been abused to download a HTML file that executed malicious JavaScript code in the context of the Label Studio website. Executing arbitrary JavaScript could result in an attacker performing malicious actions on Label Studio users if they visit the crafted avatar image. For an example, an attacker can craft a JavaScript payload that adds a new Django Super Administrator user if a Django administrator visits the image.\n\n`data_import/uploader.py` lines 125C5 through 146 showed that if a URL passed the server side request forgery verification checks, the contents of the file would be downloaded using the filename in the URL. The downloaded file path could then be retrieved by sending a request to `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` where `{project_id}` was the ID of the project and `{download_id}` was the ID of the downloaded file. Once the downloaded file path was retrieved by the previous API endpoint, `data_import/api.py`lines 595C1 through 616C62 demonstrated that the `Content-Type` of the response was determined by the file extension, since `mimetypes.guess_type` guesses the `Content-Type` based on the file extension. Since the `Content-Type` was determined by the file extension of the downloaded file, an attacker could import in a `.html` file that would execute JavaScript when visited.\n\nVersion 1.10.1 contains a patch for this issue. Other remediation strategies are also available. For all user provided files that are downloaded by Label Studio, set the `Content-Security-Policy: sandbox;` response header when viewed on the site. The `sandbox` directive restricts a page\u0027s actions to prevent popups, execution of plugins and scripts and enforces a `same-origin` policy. Alternatively, restrict the allowed file extensions that may be downloaded."
},
{
"lang": "es",
"value": "Label Studio, una herramienta de etiquetado de datos de c\u00f3digo abierto, ten\u00eda una funci\u00f3n de importaci\u00f3n remota que permit\u00eda a los usuarios importar datos desde una fuente web remota, que se descargaba y se pod\u00eda ver en el sitio web. Antes de la versi\u00f3n 1.10.1, se pod\u00eda abusar de esta caracter\u00edstica para descargar un archivo HTML que ejecutaba c\u00f3digo JavaScript malicioso en el contexto del sitio web de Label Studio. La ejecuci\u00f3n de JavaScript arbitrario podr\u00eda provocar que un atacante realice acciones maliciosas en los usuarios de Label Studio si visitan la imagen de avatar creada. Por ejemplo, un atacante puede crear un payload de JavaScript que agregue un nuevo usuario de Superadministrador de Django si un administrador de Django visita la imagen. Las l\u00edneas 125C5 a 146 de `data_import/uploader.py` mostraban que si una URL pasaba las verificaciones de verificaci\u00f3n de server side request forgery, el contenido del archivo se descargar\u00eda usando el nombre de archivo en la URL. La ruta del archivo descargado podr\u00eda recuperarse enviando una solicitud a `/api/projects/{project_id}/file-uploads?ids=[{download_id}]` donde `{project_id}` era el ID del proyecto y `{ download_id}` era el ID del archivo descargado. Una vez que el endpoint API anterior recuper\u00f3 la ruta del archivo descargado, las l\u00edneas `data_import/api.py` 595C1 a 616C62 demostraron que el `Content-Type` de la respuesta estaba determinado por la extensi\u00f3n del archivo, ya que `mimetypes.guess_type` adivina el `Tipo de contenido` basado en la extensi\u00f3n del archivo. Dado que el \"Tipo de contenido\" estaba determinado por la extensi\u00f3n del archivo descargado, un atacante podr\u00eda importar un archivo \".html\" que ejecutar\u00eda JavaScript cuando lo visitara. La versi\u00f3n 1.10.1 contiene un parche para este problema. Tambi\u00e9n se encuentran disponibles otras estrategias de remediaci\u00f3n. Para todos los archivos proporcionados por el usuario que Label Studio descarga, configure el encabezado de respuesta `Content-Security-Policy: sandbox;` cuando se vea en el sitio. La directiva `sandbox` restringe las acciones de una p\u00e1gina para evitar ventanas emergentes, la ejecuci\u00f3n de complementos y scripts y aplica una pol\u00edtica de `mismo origen`. Alternativamente, restrinja las extensiones de archivos permitidas que se pueden descargar."
}
],
"id": "CVE-2024-23633",
"lastModified": "2024-11-21T08:58:02.923",
"metrics": {
"cvssMetricV31": [
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 4.7,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "NONE",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:N/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 1.4,
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"cvssData": {
"attackComplexity": "LOW",
"attackVector": "NETWORK",
"availabilityImpact": "NONE",
"baseScore": 6.1,
"baseSeverity": "MEDIUM",
"confidentialityImpact": "LOW",
"integrityImpact": "LOW",
"privilegesRequired": "NONE",
"scope": "CHANGED",
"userInteraction": "REQUIRED",
"vectorString": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N",
"version": "3.1"
},
"exploitabilityScore": 2.8,
"impactScore": 2.7,
"source": "nvd@nist.gov",
"type": "Primary"
}
]
},
"published": "2024-01-24T00:15:08.373",
"references": [
{
"source": "security-advisories@github.com",
"tags": [
"Not Applicable"
],
"url": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox"
},
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62"
},
{
"source": "security-advisories@github.com",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146"
},
{
"source": "security-advisories@github.com",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Not Applicable"
],
"url": "https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Content-Security-Policy/sandbox"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/api.py#L595C1-L616C62"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Product"
],
"url": "https://github.com/HumanSignal/label-studio/blob/1.9.2.post0/label_studio/data_import/uploader.py#L125C5-L146"
},
{
"source": "af854a3a-2127-422b-91ae-364da2661108",
"tags": [
"Third Party Advisory"
],
"url": "https://github.com/HumanSignal/label-studio/security/advisories/GHSA-fq23-g58m-799r"
}
],
"sourceIdentifier": "security-advisories@github.com",
"vulnStatus": "Modified",
"weaknesses": [
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "security-advisories@github.com",
"type": "Secondary"
},
{
"description": [
{
"lang": "en",
"value": "CWE-79"
}
],
"source": "nvd@nist.gov",
"type": "Primary"
}
]
}