ghsa-26w3-q4j8-4xjp
Vulnerability from github
Published
2024-03-06 15:29
Modified
2025-02-11 19:03
Severity ?
VLAI Severity ?
Summary
1Panel open source panel project has an unauthorized vulnerability.
Details
Impact
The steps are as follows:
-
Access https://IP:PORT/ in the browser, which prompts the user to access with a secure entry point.
-
Use Burp to intercept:
When opening the browser and entering the URL (allowing the first intercepted packet through Burp), the following is displayed:
It is found that in this situation, we can access the console page (although no data is returned and no modification operations can be performed)."
Affected versions: <= 1.10.0-lts
Patches
The vulnerability has been fixed in v1.10.1-lts.
Workarounds
It is recommended to upgrade the version to 1.10.1-lts.
References
If you have any questions or comments about this advisory:
Open an issue in https://github.com/1Panel-dev/1Panel Email us at wanghe@fit2cloud.com
{
"affected": [
{
"database_specific": {
"last_known_affected_version_range": "\u003c= 1.10.0-lts"
},
"package": {
"ecosystem": "Go",
"name": "github.com/1Panel-dev/1Panel"
},
"ranges": [
{
"events": [
{
"introduced": "0"
},
{
"fixed": "1.10.1-lts"
}
],
"type": "ECOSYSTEM"
}
]
}
],
"aliases": [
"CVE-2024-27288"
],
"database_specific": {
"cwe_ids": [
"CWE-863"
],
"github_reviewed": true,
"github_reviewed_at": "2024-03-06T15:29:11Z",
"nvd_published_at": "2024-03-06T19:15:07Z",
"severity": "MODERATE"
},
"details": "### Impact\n\nThe steps are as follows:\n\n1. Access https://IP:PORT/ in the browser, which prompts the user to access with a secure entry point.\n\n\n2. Use Burp to intercept:\n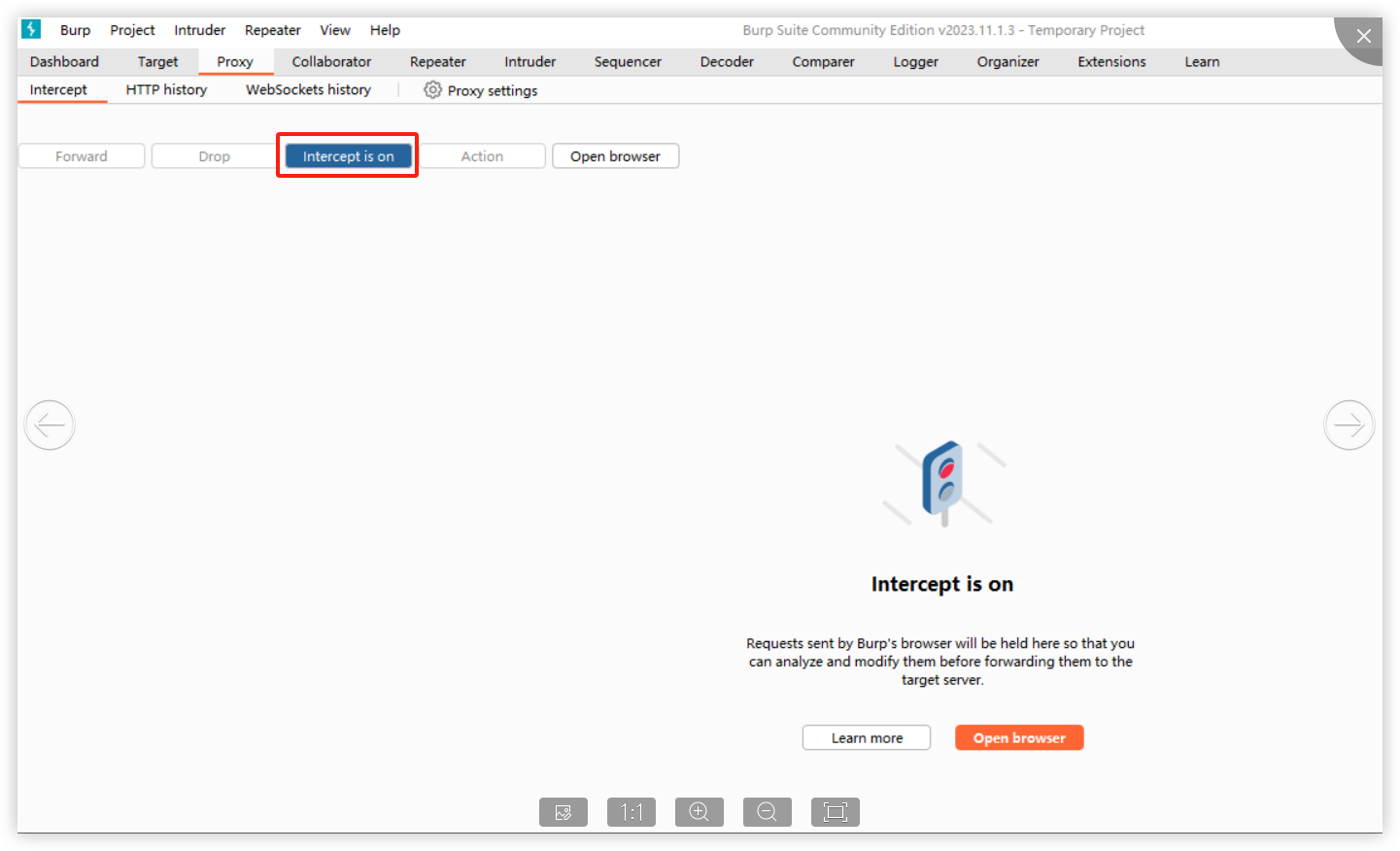\n\nWhen opening the browser and entering the URL (allowing the first intercepted packet through Burp), the following is displayed:\n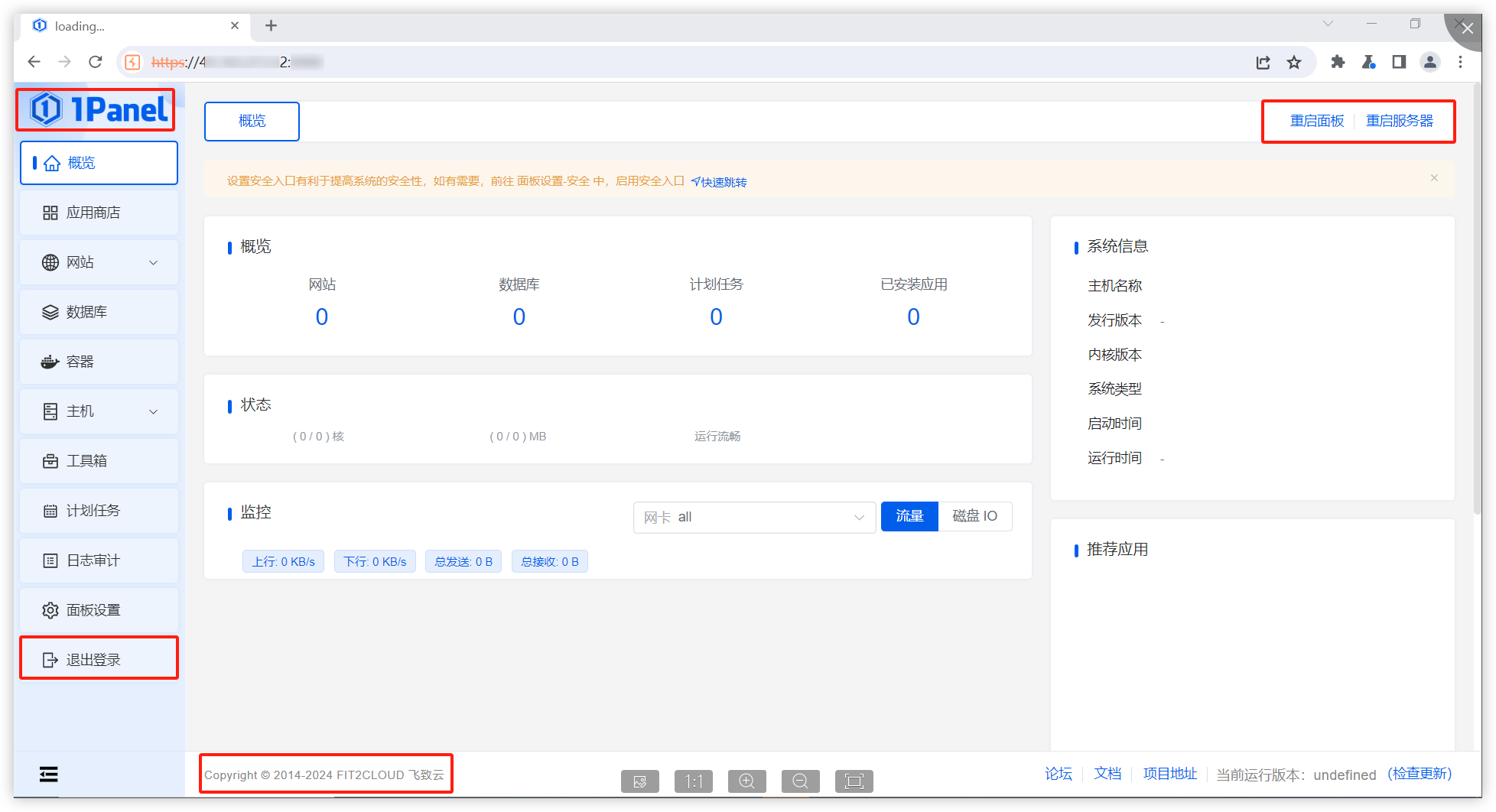\n\nIt is found that in this situation, we can access the console page (although no data is returned and no modification operations can be performed).\"\n\nAffected versions: \u003c= 1.10.0-lts\n\n### Patches\n\nThe vulnerability has been fixed in v1.10.1-lts.\n\n### Workarounds\n\nIt is recommended to upgrade the version to 1.10.1-lts.\n\n### References\n\nIf you have any questions or comments about this advisory:\n\nOpen an issue in https://github.com/1Panel-dev/1Panel\nEmail us at wanghe@fit2cloud.com",
"id": "GHSA-26w3-q4j8-4xjp",
"modified": "2025-02-11T19:03:36Z",
"published": "2024-03-06T15:29:11Z",
"references": [
{
"type": "WEB",
"url": "https://github.com/1Panel-dev/1Panel/security/advisories/GHSA-26w3-q4j8-4xjp"
},
{
"type": "ADVISORY",
"url": "https://nvd.nist.gov/vuln/detail/CVE-2024-27288"
},
{
"type": "WEB",
"url": "https://github.com/1Panel-dev/1Panel/pull/4014"
},
{
"type": "PACKAGE",
"url": "https://github.com/1Panel-dev/1Panel"
},
{
"type": "WEB",
"url": "https://github.com/1Panel-dev/1Panel/releases/tag/v1.10.1-lts"
}
],
"schema_version": "1.4.0",
"severity": [
{
"score": "CVSS:3.1/AV:N/AC:L/PR:N/UI:R/S:U/C:L/I:L/A:L",
"type": "CVSS_V3"
}
],
"summary": "1Panel open source panel project has an unauthorized vulnerability."
}
Loading…
Loading…
Sightings
| Author | Source | Type | Date |
|---|
Nomenclature
- Seen: The vulnerability was mentioned, discussed, or seen somewhere by the user.
- Confirmed: The vulnerability is confirmed from an analyst perspective.
- Exploited: This vulnerability was exploited and seen by the user reporting the sighting.
- Patched: This vulnerability was successfully patched by the user reporting the sighting.
- Not exploited: This vulnerability was not exploited or seen by the user reporting the sighting.
- Not confirmed: The user expresses doubt about the veracity of the vulnerability.
- Not patched: This vulnerability was not successfully patched by the user reporting the sighting.
Loading…
Loading…